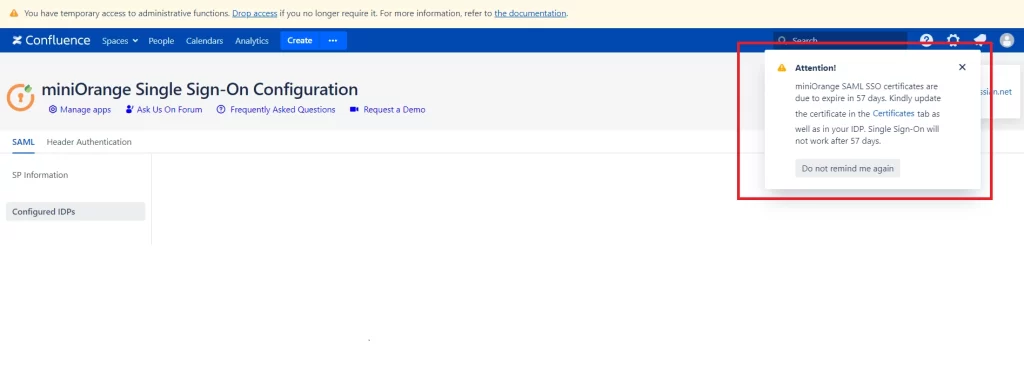
If you see the warning notification above, it indicates that the plugin’s certificate is going to expire in the next few days. This certificate is used to sign SAML authentication requests and encrypt/decrypt SAML responses from the IDP. You may ignore the warning if you are not using the abovementioned configuration, however, it is recommended that you update the certificate by configuring your own X.509 certificate or generating a new one directly from the plugin.
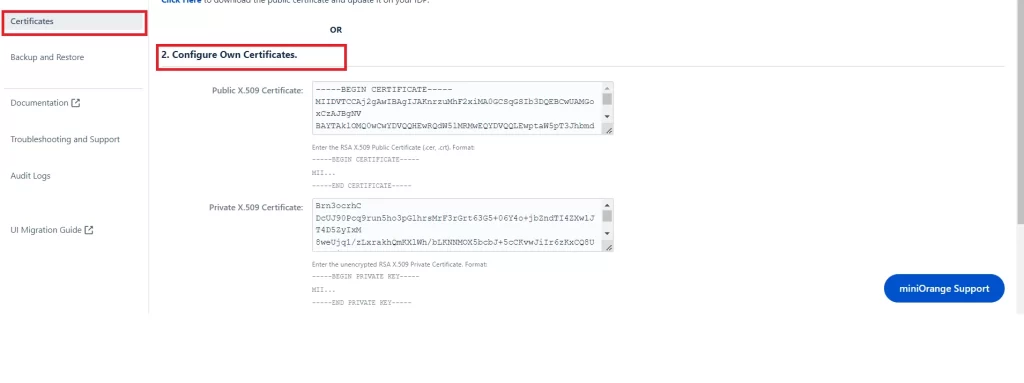
You will find the mentioned certificates in the Plugin Configuration –> Certificate menu and the procedures are described below.
- Schedule downtime.
- Verify functioning SSO.
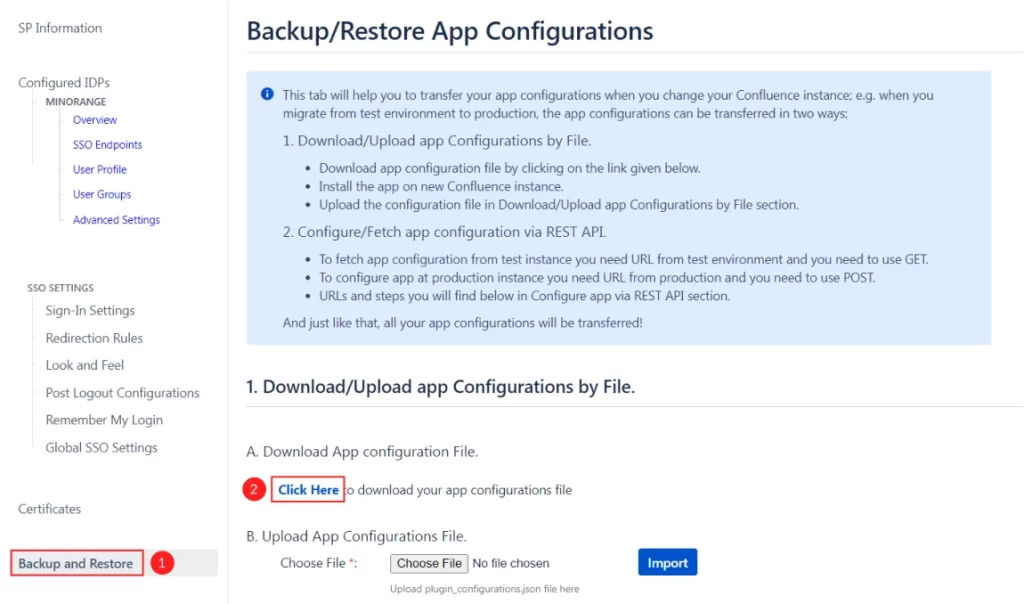
- Go to Backup/Restore Configurations tab and download the App configuration file for backup.
-
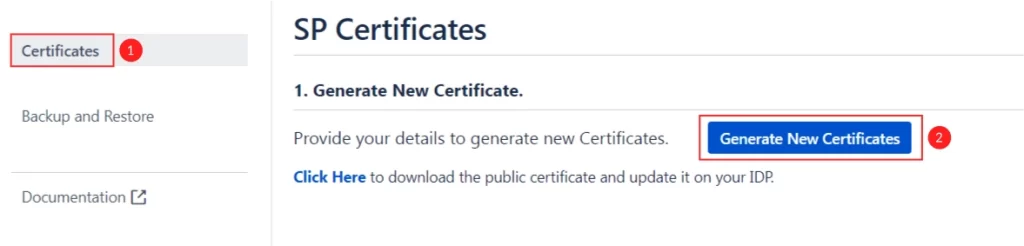
Go to the Certificates tab and copy the current public and private keys to the notepad. Save it and keep it as a backup.
-
Click on Generate New Certificates. Enter relevant details and generate new certificates.
- Go to Service Provider Info and from the table, against Certificate click on the Download button.
- Configure this certificate in the Identity Provider.
- Confirm correct certificate migration using Test Configuration (Configure IDP tab, next to Save). You should see a success message. If you get a certificate mismatch error, follow steps 4 to 6 again.

- Open a new browser to test SSO.
-
In case of any issues, you can restore the older certificate using the below methods.
-
Using the saved backup of private and public keys: Use the previously copied public and private keys and paste it again into the Configure Own Certificates option of the Certificates tab as shown in the screenshot below.
-
- You can also restore the settings with a single click. In the certificates tab, you will find an option as “Click Here to restore the default certificate”. Click on the link to revert back to the original certificates.
- If you still face an issue, please contact support-atlassian@miniorange.atlassian.net or raise a support request from here.